Structured Query Language, commonly known as SQL, is the bedrock for data manipulation and retrieval in relational databases.
In the realm of data science, SQL’s significance cannot be overstated as it provides the foundational tools for data scientists to cleanse, manipulate, and analyze large sets of data efficiently.
The power of SQL lies in its capability to communicate with databases, allowing for the extraction of meaningful insights from raw data.
Its importance is recognized by both academia and industry, with SQL continuing to be a core component of data science education and practice.

The versatility of SQL is showcased through its widespread application across various domains where data science plays a crucial role.
Data scientists regularly utilize SQL to perform tasks such as data cleaning, data wrangling, and analytics, which are essential for making data useful for decision-making.
Mastery of SQL gives data scientists the advantage of directly interacting with databases, thus streamlining the data analysis process.
As such, SQL serves as a critical tool for converting complex data into actionable knowledge, underpinning the development of data-driven solutions.
Understanding SQL is also crucial for the implementation of machine learning models, since SQL facilitates the construction of datasets needed for training algorithms.
The language’s relevance extends to the creation of scalable data infrastructures, further emphasizing its role as an enabler for the innovative use of data in science and technology.
With the increasing centrality of data in modern enterprises, SQL continues to be a key skill for data professionals aiming to deliver valuable insights from ever-growing data ecosystems.
Fundamentals of SQL for Data Science
SQL, or Structured Query Language, is essential for manipulating and querying data in relational databases.
Data scientists utilize SQL to access, clean, and prepare data for analysis.
Understanding SQL Syntax
SQL syntax is the set of rules that define the combinations of symbols and keywords that are considered valid queries in SQL.
Queries often begin with SELECT, FROM, and WHERE clauses to retrieve data matching specific conditions.
The syntax is consistent and allows for a variety of operations on database data.
Data Types and Structures in SQL
SQL databases are organized in tables, consisting of rows and columns.
Each column is designed to hold data of a specific data type such as integer, float, character, or date.
Understanding these data types is vital, as they define how data can be sorted, queried, and connected within and across tables.
SQL Operations and Commands
A range of SQL operations and commands enables data scientists to interact with databases.
Common operations include:
- SELECT: Extracts data from a database.
- UPDATE: Modifies the existing records.
- INSERT INTO: Adds new data to a database.
- DELETE: Removes data from a database.
Each command is a building block that, when combined, can perform complex data manipulations necessary for data analysis.
Data Manipulation and Management
In the realm of data science, SQL is a cornerstone for effectively handling data. It empowers users to interact with stored information, making it a vital skill for data manipulation and management tasks.
Data Querying
SQL is renowned for its powerful querying capabilities.
By utilizing SELECT statements, data scientists can retrieve exactly the data they require from large and complex databases. The WHERE clause further refines this by allowing for precise filtering.
- Retrieve data:
SELECT * FROM table_name; - Filter results:
SELECT column1, column2 FROM table_name WHERE condition;
Data Insertion
To add new records to a database, SQL employs the INSERT INTO statement.
This is crucial for expanding datasets in a systematic manner. Before analysts can query or manipulate data, it must first be properly inserted into the database.
- Insert single record:
INSERT INTO table_name (column1, column2) VALUES (value1, value2); - Insert multiple records:
INSERT INTO table_name (column1, column2) VALUES (value1, value2), (value3, value4);
Data Update and Deletion
SQL commands UPDATE and DELETE play critical roles in maintaining database integrity and relevance.
The UPDATE statement is employed to modify existing records. Concurrently, DELETE is used to remove unwanted data, keeping databases efficient and up-to-date.
- Update records:
UPDATE table_name SET column1 = value1 WHERE condition; - Delete records:
DELETE FROM table_name WHERE condition;
SQL commands for data manipulation are essential for managing the lifecycle of data within any database, ensuring that datasets remain current and accurate for analysis.
SQL in Data Analysis
SQL is a cornerstone in data analysis for its robust functionality in data manipulation and retrieval. It enables analysts to interact efficiently with large databases, making it indispensable for data-driven decision-making.
Aggregating Data
In data analysis, aggregating data is crucial to summarize information and extract meaningful insights.
SQL provides functions such as SUM(), AVG(), COUNT(), MAX(), and MIN() that allow users to perform calculations across rows that share common attributes.
Analysts rely on these aggregations to condense datasets into actionable metrics.
SUM()computes the total of a numeric column.AVG()calculates the average value in a set.COUNT()returns the number of rows that satisfy a certain condition.MAX()andMIN()find the highest and lowest values, respectively.
Data Sorting and Filtering
To enhance the readability and relevance of data, data sorting and filtering are vital.
SQL’s ORDER BY clause sorts retrieved data by specified columns, either in ascending or descending order, aiding in organizing results for better interpretation.
The WHERE clause filters datasets based on specified criteria, thus enabling analysts to isolate records that meet certain conditions and disregard irrelevant data.
ORDER BY column_name ASC|DESCsorts rows alphabetically or numerically.WHERE conditionfilters records that fulfill a particular condition.
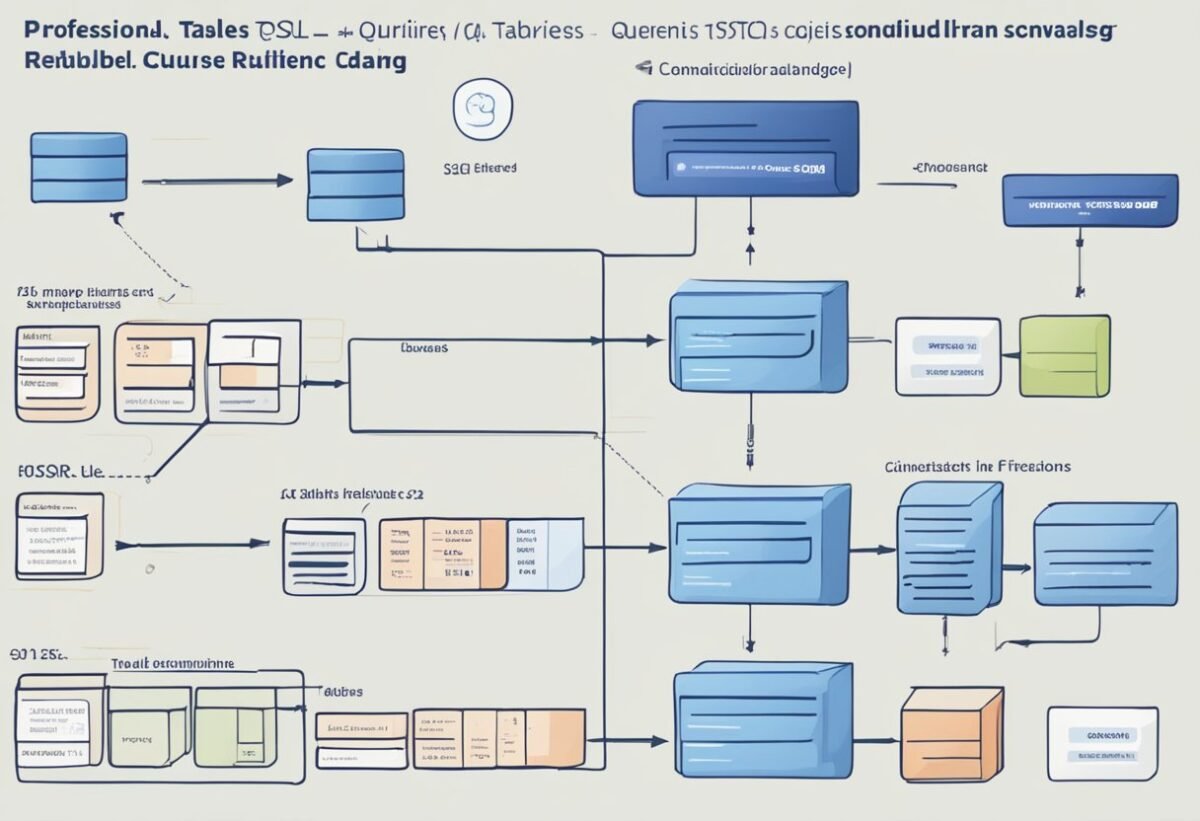
Joining Multiple Data Sources
SQL excels at joining multiple data sources, a technique pivotal for comprehensive analysis when datasets are housed in separate tables.
By using JOIN clauses, one can merge tables on common keys, juxtaposing related data from various sources into a single, queryable dataset.
Types of joins like INNER JOIN, LEFT JOIN, RIGHT JOIN, and FULL OUTER JOIN give analysts the flexibility to choose how tables relate to one another.
INNER JOINreturns rows when there is at least one match in both tables.LEFT JOINincludes all rows from the left table, with matching rows from the right table.RIGHT JOINandFULL OUTER JOINoperate similarly but with emphasis on the right table, or both tables, respectively.
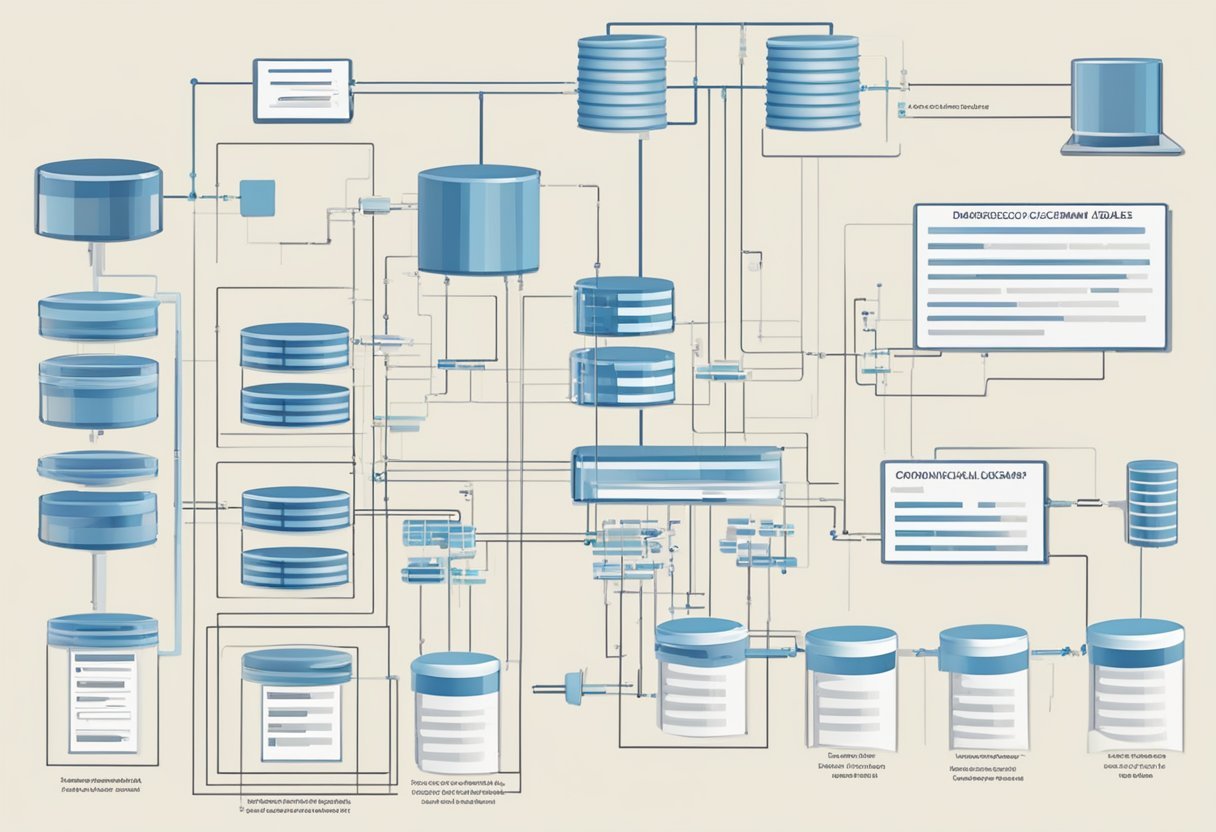
Database Design and Normalization
Within the realm of data science, efficient database design and normalization are pivotal. They ensure the integrity and optimality of a database by organizing data to reduce redundancy and enhance data retrieval.
Schema Design
Schema design is the first crucial step in structuring a database. A well-planned schema underpins a database’s performance and scalability.
The goal is to design a schema that can handle a variety of data without inefficiency, which can be achieved through normal forms and normalization.
For example, a normalization algorithm plays a critical role in eliminating redundant data, ensuring schemas are free from unnecessary repetition.
Indexing
Indexing proves indispensable in optimizing data retrieval. It functions much like an index in a book, allowing faster access to data.
However, one must employ indexing judiciously. Over-indexing leads to increased storage and can negatively impact write operations performance, while under-indexing can leave the system sluggish during queries.
Mastering the use of indexes is a subtle art crucial for database efficiency, tying in closely with the schema to ensure a balanced and efficient database system.
SQL Optimization Techniques
Optimizing SQL is pivotal in data science to enhance query performance and ensure efficient data management. Rigorous optimization techniques are the backbone for responsive data analysis.
Query Performance Tuning
In query performance tuning, the focus is on framing SQL statements that retrieve results swiftly and efficiently.
Data scientists often use EXPLAIN statements to understand how the database will execute a query.
Additionally, avoiding unnecessary columns in the SELECT statement and using WHERE clauses effectively can lead to more focused and hence faster queries.
Efficient Data Indexing
Efficient data indexing is crucial for improving query performance.
By creating indexes on columns that are frequently used in the WHERE clause or as join keys, databases can locate the required rows more quickly.
It is important to consider the balance between having necessary indexes for query optimization and having too many, which may slow down insert and update operations.
Execution Plans and Caching
Understanding execution plans is key for identifying bottlenecks in query performance.
Data scientists can interpret these plans to modify queries accordingly.
Furthermore, implementing caching strategies where commonly retrieved data is stored temporarily can significantly improve query response time.
Servers can serve cached results for common queries instead of re-executing complex searches.
Integrating SQL with Other Tools
SQL’s versatility allows it to enhance data science processes when combined with other tools. It serves as a robust foundation for various integrations, enabling more sophisticated analysis and data management.
SQL and Spreadsheet Software
Integrating SQL with spreadsheet applications like Excel enables users to manage larger datasets that spreadsheets alone could handle inefficiently.
Functions such as importing SQL queries into a spreadsheet or using SQL to automate the manipulation of data in Excel provide a powerful extension to the spreadsheet’s native capabilities.
SQL and Programming Languages
SQL’s integration with programming languages such as Python or R amplifies data science capabilities.
For example, Python offers libraries like pandas for data analysis and sqlalchemy for database management. These libraries allow SQL queries to be executed directly from the Python environment. As a result, workflows are streamlined and complex data manipulations are enabled.
SQL in Business Intelligence Tools
In business intelligence (BI) platforms, SQL plays a critical role in querying databases and generating reports.
Platforms such as Tableau or Power BI utilize SQL to extract data. This allows users to create interactive dashboards and visualizations that support data-driven decision-making.
Data Security and SQL
Data security within SQL-driven environments is crucial for safeguarding sensitive information.
It ensures that data is accessible only to authorized users and is protected against unauthorized access and threats.
Access Control
Access control is the process of determining and enforcing who gets access to what data within a database.
SQL implements access control via Data Control Language (DCL) commands such as GRANT and REVOKE. These commands are used to give or take away permissions from database users.
Data Encryption
Data encryption in SQL databases involves transforming data into a secured form that unauthorized parties cannot easily comprehend.
Encryption can be applied to data at rest, using methods like Transparent Data Encryption (TDE). It can also be applied to data in transit with Secure Sockets Layer (SSL) or Transport Layer Security (TLS).
SQL Injection Prevention
SQL injection is a technique where an attacker exploits vulnerabilities in the SQL code layer to execute malicious queries.
Preventative measures include using parameterized queries and stored procedures, which help ensure that SQL commands are not altered by user input.
Running regular security audits and keeping systems updated with security patches are also key strategies for SQL injection prevention.
Frequently Asked Questions

In the realm of data science, Structured Query Language (SQL) is integral for the efficient handling of data. This section aims to address some common inquiries regarding its importance and utility.
What role does SQL play in managing and querying large datasets for data analysis?
SQL is the standard language used to retrieve and manipulate data stored in relational databases.
It enables data scientists to handle large volumes of data by running complex queries and aggregations which are pivotal for data analysis.
How does knowledge of SQL contribute to the effectiveness of a data scientist’s skill set?
Proficiency in SQL enhances a data scientist’s ability to directly access and work with data.
This direct engagement with data allows for a more profound understanding of datasets, leading to more accurate analyses and models.
Why is SQL considered a critical tool for performing data manipulations in data science?
SQL is essential for data science tasks as it allows for precise data manipulations.
Through SQL commands, data scientists can clean, transform, and summarize data, which are crucial steps before any data analysis or machine learning can be applied.
How can SQL skills enhance a data scientist’s ability to extract insights from data?
SQL skills empower a data scientist to efficiently sort through and query data, enabling the extraction of meaningful insights.
These skills are vital for interpreting data trends and making data-driven decisions.
What are the advantages of using SQL over other programming languages in data-driven projects?
SQL’s syntax is specifically designed for managing and querying databases, making it more streamlined and easier to use for these tasks than general-purpose programming languages.
This specialization often results in faster query performance and reduced complexity in data-driven projects.
In what ways does the mastery of SQL impact the efficiency of data cleaning and preprocessing?
Mastery of SQL can significantly expedite data cleaning and preprocessing.
With advanced SQL techniques, data scientists can quickly identify and rectify data inconsistencies.
They can also streamline data transformation and prepare datasets for analysis in a more time-effective manner.